The internet is filled with illegal applications, cracks, games, movies, TV rips, e-books - collectively referred to as warez. There are many ways to obtain warez from usenet, torrent sites, rapidshare, and many others. Today we will share some knowledge on how to search the internet for warez.
ANIME
One of the best places to start searching for anime is AnimeDB. It has a database of nearly every anime ever released. Find the anime you are looking for using the search bar. Each anime has it's own page where you can view all the groups that are releasing that particular show.
Lots of useful information such as languages, comments, ratings of each group allows you to choose which group to download from. From there follow the link to the group's site to download.
CRACKS
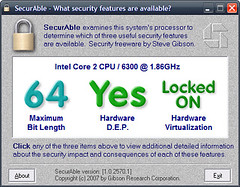
If you are searching for software cracks, then Astalavista has a useful search engine of the major warez sites. Be careful though as many sites are filled with malware. Make sure your browser is sandboxed using Sandboxie or DefenseWall.
Always search for serials or keygens first as some cracks contain malware. Be sure to scan it first with your anti-virus. For extra precaution, scan the files online with VirusTotal or Jotti Scanner.
E-BOOKS
A good e-book search engine is eBdb. It indexes several major e-book sites as well as many obscure sites (usually Russian - use Google Translate).
TORRENTS
There are several useful torrent search engines. The most famous is isoHunt. It indexes most of the major torrent sites and has a very good search engine. Due to legal troubles however, isoHunt's days appear to be numbered.
Another torrent search engine is Torrent Finder. It takes a different approach to isoHunt, in that it is a meta-search engine, allowing you to choose which sites to search and then presenting the original sites in a tabbed interface. Very useful but slow.
If you fancy searching via Google Custom Search, someone has already created a Google Custom Torrent Search here. It searches 50 sites, uses Google search but may not be that updated.
If you are still stumped then two sites provide an index of sites. Both group sites into categories. They can be found here and here.
ONLINE STORAGE
Several online storage sites allows you to store any kind of file and for anyone to download them. MyBloop is catered towards, but not limited to, music - has unlimited storage, allows you to listen to songs for free and using this hack allows you to download them.
Many of the file upload sites such as Rapidshare, MegaUpload and others hosts warez files. Again Google Custom Search allows you to search for warez on 127 such sites. Or you could always search in Google for the file you want, let's say Harry Potter, like this: "Harry Potter" rapidshare. Replace rapidshare with any other upload site.
SEARCH
There are many other techniques for searching for warez using Google. Several sites has streamlined the process and provided their own search engine. Briefli searches Google for audio, video, torrent and office. It even provides a manual edit.
Meanwhile G2P uses Google to search for songs, albums, software, e-books, ringtones and proxies.
FTP
To search FTP directories, proceed to FileWatcher or MetaFTP. Searching for files in FTP is much harder and usually a waste of time.
Hope you enjoy this little tutorial. Of course more warez can be found in forums but that's all for now. And be sure to practice safe warez-ing.